NIST 800-53, Meet Arpio: Resilience With Rapid Compliance:
NIST SP 800-53 is the grand control catalog that powers programs like FISMA and FedRAMP. It tells you what good looks like across security and resilience, then asks for proof. This post is the Cliff-notes version that you, your CISO, SRE lead, and auditor can all read without needing a nap afterwards.
The 90-Second NIST 800-53 Refresher
What it is: A comprehensive catalog of security and privacy controls for systems and organizations.
How it is Organized: Control families like Access Control (AC), Audit and Accountability (AU), Contingency Planning (CP), Incident Response (IR), Risk Assessment (RA), Supply Chain Risk (SR), and more.
How You Scope It: Apply baseline rigor by impact level. Low. Moderate. High.
What it Wants: Documented plans, tested continuity, measurable outcomes, and evidence that the controls you say you have actually work.
Think of DORA and NIS2 as the why. NIST 800-53 is the how. It is the recipe that keeps your 6 tier-cake standing when someone slams the door.
Where Teams Stumble in Real Life:
Backups are Not Recovery. Teams have snapshots. They do not have a reliable way to reassemble apps, networks, endpoints, and secrets into a working service.
Tests That Do Not Match Reality. Environments change. The last DR drill resurrected a 6-month old design that users no longer recognize.
Evidence After the Fact. Control owners start hunting for logs and screenshots the morning the audit starts.
Distributed Responsibility Without an Orchestration Spine. Infra, security, and app owners all own a slice. Nobody owns a push button that proves the ingredients bake into a cake.
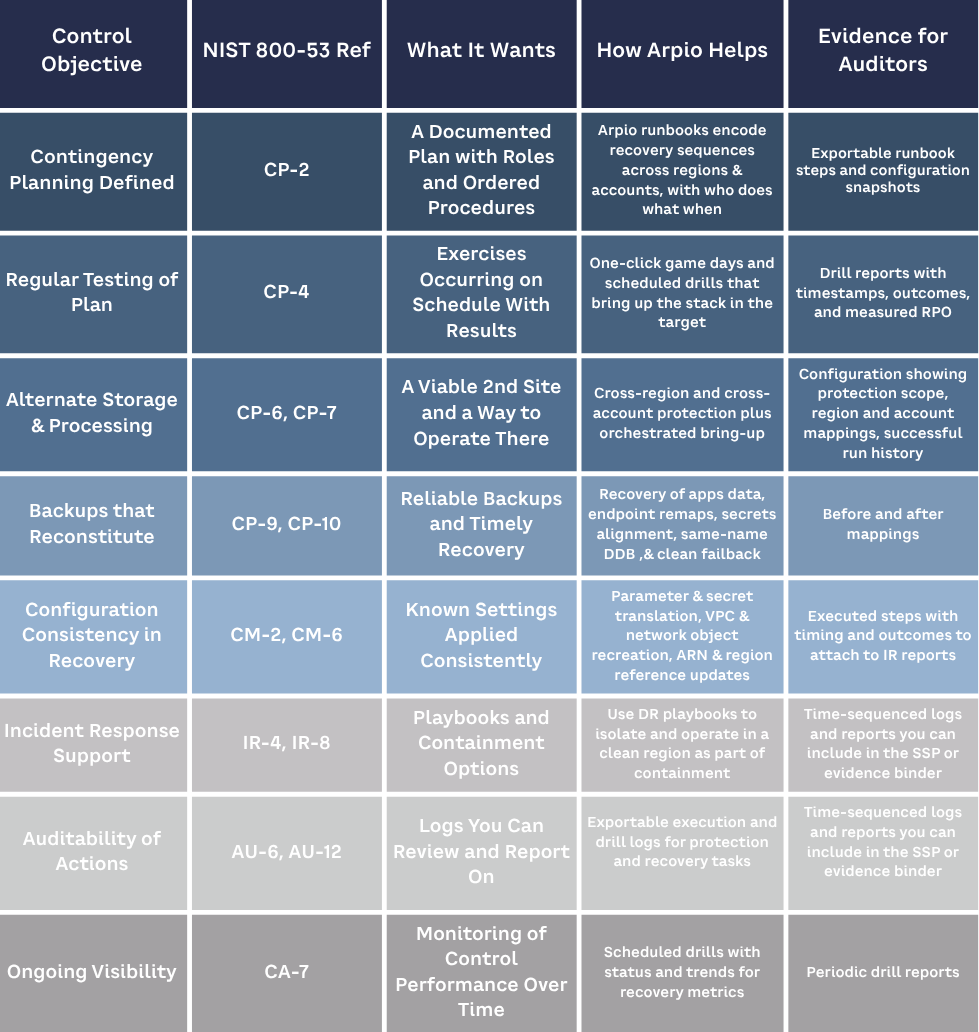
How Arpio turns NIST 800-53 Requirements Into Deliverables
Arpio automates application recovery across AWS accounts and regions, with optional ransomware elimination. It discovers resources, maps dependencies, translates environment specifics, and executes recovery flows that are repeatable and safe to run multiple times. Then it gives you the artefacts your auditors keep asking for.
Below are the controls where Arpio is your force multiplier. I am using the Rev. 5 control names so your compliance team can nod vigorously.
Contingency Planning (CP)
CP-2 Contingency Plan
Arpio codifies recovery policies from your live environment. You set RPO targets, choose target region or account, and define recovery plans. Result: a living plan that is tied to real resources, not a Word doc that ages like milk.
CP-4 Contingency Plan Testing
Run non-disruptive drills on demand. Arpio brings up a recovery environment, runs health checks, validates endpoints, then tears it down. You keep time-stamped results and a resource inventory for each test.
CP-6 Alternate Storage Site and CP-7 Alternate Processing Site
Recover to another AWS region or account. Arpio handles the gritty details like VPCs, subnets, routes, target groups, and security groups so traffic actually flows.
CP-9 System Backup and CP-10 System Recovery and Reconstitution
Use existing snapshots and backups, then orchestrate the full resurrection. Compute, data, configuration, and the connective tissue that makes the app behave like the app.
Incident Response and Auditability
IR-4 Incident Handling
A recovery run becomes a chronological action trail. Who initiated, what was executed, which checks passed, and when service came back. That timeline drops neatly into incident reports.
AU-6 Audit Review, Analysis, and Reporting
Export drill and incident artefacts for your GRC or SIEM. Arpio is not your SIEM. It is the source of clean, contextual recovery evidence that feeds one.
Risk and Supply Chain Context
RA-3 and RA-5 Risk Assessment and Vulnerability Monitoring
Arpio does not scan for CVEs. It does give you an up-to-date inventory and recovery feasibility that feeds risk analysis. You can show what is recoverable today and where the gaps are.
SR-3 and SR-11 Supply Chain Risk
NIST wants you to manage provider risk and maintain continuity if a dependency sneezes. Arpio’s cross-account and cross region recovery supports exit and fallback strategies you can point to with a straight face.
Translation Magic That Makes This Practical:
Endpoint Continuity with Private Hosted Zones or DNS updates so apps talk to the recovered resources without rename gymnastics.
Secrets History Sync so recovered databases accept the credentials your apps actually use today.
Name and ARN Translation so dependent services reference the right things in the new region or account.
Network Remap so the VPC, subnets, routes, security groups, and target groups are recreated consistently.
Failback to send workloads home after the dust settles, using the same policy and checks.