DORA, Meet Arpio: Resilience With Rapid Compliance:
If you work in European finance or provide services to companies that are, DORA is no longer a comet in the distance. It’s now in orbit, waving at the dinosaurs. The Digital Operational Resilience Act (DORA) is here, and it raises the bar on how financial entities plan, test, and prove their ability to withstand ICT disruption.
You should care about DORA because non-compliance can cost you up to 2% of your total annual worldwide turnover, or €5 million per breach – whichever makes your CFO sweat more.
These are the flash cards: what DORA actually expects, who’s affected (spoiler: more than you think), and how Arpio helps you ship genuine resilience while handing auditors neat, exportable proof. That last part is our favorite phrase: rapid compliance – because with Arpio, you can show evidence immediately after deployment, not six quarters from now when everyone’s already changed jobs because of a breach.
What Exactly are “ICTs” in DORA?
Short answer: pretty much everything that keeps your digital business standing upright.
Long answer: DORA defines ICT services as digital and data services delivered through ICT systems on an ongoing basis – including cloud (IaaS, PaaS, SaaS), data centers, managed networks, software, and even hardware-as-a-service or vendor support via firmware/software updates. (It explicitly excludes analogue telephony, so your fax machine’s off the hook. For now.) The definition is intentionally broad – if it keeps the lights on for your apps, it counts.
Who’s Actually in Scope (and Why Suppliers Should Care):
Financial entities in the EU: banks, insurers/reinsurers, investment firms, payment and e-money institutions, brokers, and yes – even crypto-asset service providers. If you’re regulated in EU finance, DORA applies from 17 January 2025.
ICT third-party service providers (your vendors): even if you’re not “critical,” you’re affected indirectly because financial entities must impose mandatory contractual clauses, maintain a register of all ICT arrangements, and demand testing, audit rights, reporting, and exit plans. If a provider is deemed critical, it also comes under direct EU oversight by the ESAs (EBA/ESMA/EIOPA).
Even if you’re not in finance, if you provide ICT services to companies that are, DORA follows you too – because their compliance obligations become your contractual obligations.
Translation: if you sell tech or services to finance, you’re going to feel DORA – by contract at minimum, and possibly by regulator spotlight. And yes, this applies even if you’re outside Europe (say, in the US). If your systems touch EU-regulated financial entities, surprise! – you’re in scope.
The 90-second DORA refresher
DORA focuses on five big buckets:
ICT risk management
Incident reporting and management
Digital operational resilience testing (including threat-led testing for some entities)
ICT third-party risk
Information sharing
Where Teams Stumble in Real Life:
A region hiccups and your “manual DR runbook” turns into a choose-your-own-adventure book.
Endpoints change, secrets drift, and suddenly “the database is up” but every app still points at Frankfurt.
You test once a year on a sandbox no one trusts, then cannot prove the thing you tested is the thing you run.
Auditors ask for evidence tied to specific controls and dates. You provide a heroic story and three screenshots named final_final2.png.
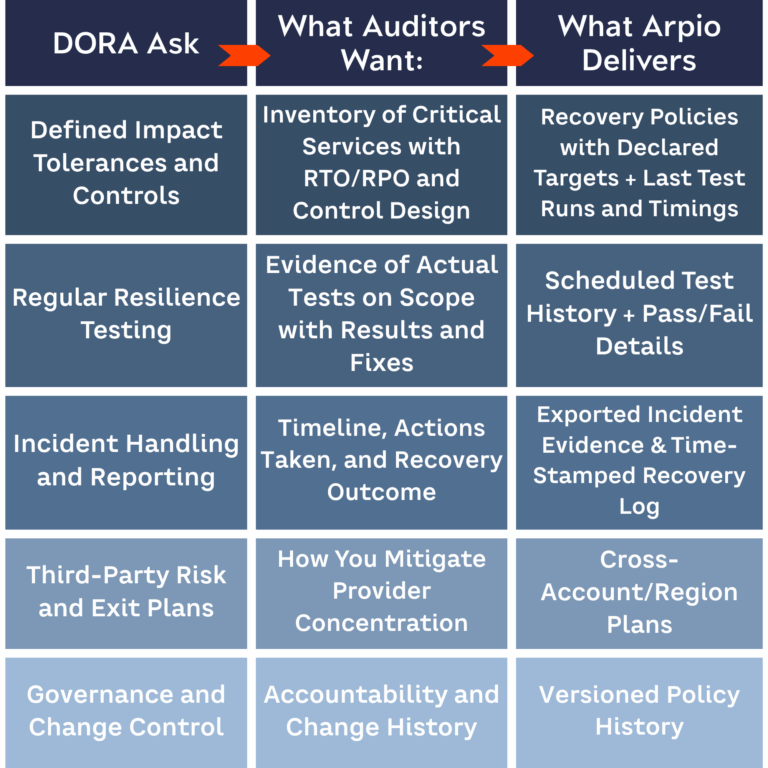
How Arpio Turns DORA Requirements Into Deliverables:
Arpio is DR-as-Chill for AWS and beyond. It discovers your workloads, maps dependencies, translates environment specifics, and automates recovery across accounts and regions. The result: consistent failover and failback you can run on demand, with evidence you can hand to an auditor without apologizing and hoping for mercy.
1) ICT Risk Management – Deterministic Recovery Plans
Auto-discovery builds a living inventory and dependency graph.
You declare guardrails (RTO, RPO, region, account, network). Arpio enforces them in recovery plans.
Logs and change history give you traceability for each recovery policy.
Why this matters for DORA: it shows you identified critical functions, defined tolerances, and put controls in place.
2) Incident Management and Reporting – Timelines You Can Export
One-click recovery creates a time-stamped trail: who initiated, what resources moved, what succeeded, and when.
Post-incident, you export an evidence pack for your report: scope, impact, actions, outcomes.
Why this matters for DORA: incident handling is not just fixing things. It’s proving what happened, when, and how you restored service.
3) Digital Operational Resilience Testing – Safe, Repeatable DR Drills
Non-disruptive tests spin up a recovery environment, validate service health, then tear down.
Schedule tests, track pass rates, compare RTO/RPO to targets, and keep an audit-ready history.
For institutions facing TLPT, Arpio supplies a realistic, isolated target for threat-led exercises and preserves evidence of outcomes.
Why this matters for DORA: regular testing with artefacts closes the “we think it works” gap.
4) Third-Party and Concentration Risk – Exit Strategy as a Control
Cross-account and cross-region recovery reduces single-account blast radius.
Multi-cloud recovery options support an exit strategy if a provider layer is impaired.
Arpio keeps a register of recovery dependencies that feeds your third-party inventory.
Why this matters for DORA: you must manage risks from your ICT providers and keep critical services running if one fails.
5) Information Sharing – Clean Signals, Not Noise
Arpio’s APIs push test and incident metadata to SIEM or GRC tools.
You can share factual indicators and recovery metrics with industry bodies without oversharing.
Why this matters for DORA: structured information enables sector-wide resilience instead of tribal stories.
“Translation Magic” That Saves Weekends:
Your world is messy. Arpio has a ‘degree’ in messy.
Endpoint Continuity: keep app endpoints working after recovery by remapping DNS or PHZ records.
Secrets History Sync: align recovered apps with the right credentials from Secrets Manager and Parameter Store.
Name and ARN Translation: rebuild resources with new names, regions, and accounts while updating dependent references.
Network Remap: recreate VPCs, subnets, routes, security groups, and target groups so traffic flows on day one, not day never.
This is the unglamorous work that turns “the instance is up” into “the service is back and ready to be used.”